Welcome to download the newest Pass4itsure 2V0-641 dumps:
We at Flydumps Cisco 640-553 exam sample questions are IT. experts and are highly experienced in the field of exam dumps and study notes as our team is continuously working for the more accomplished Cisco 640-553 exam guide and test questions. At Cisco 640-553 exam sample questions Flydumps, all the necessary Cisco 640-553 exam guide is available which not only includes free Cisco 640-553 but it also contains Cisco 640-553 study guide and Cisco 640-553 practice exam.
QUESTION 126
Which option is the term for what happens when a computer code is developed to take advantage of
vulnerability?
For example, suppose that a vulnerability exists in a piece of software, but nobody knows about this
vulnerability.
A. a vulnerability
B. a risk
C. an exploit
D. an attack
E. a joke
Correct Answer: C
QUESTION 127
What is the first step you should take when considering securing your network?
A. install a firewall
B. install an intrusion prevention system
C. update servers and user PCs with the latest patches
D. Develop a security policy
E. go drink beer and don?t worry about it
Correct Answer: D
QUESTION 128
Which option is a key principal of the Cisco Self-Defending Network strategy?
A. security is static and should prevent most know attack on the network
B. the self-defending network should be the key point of your security policy
C. integrate security throughout the existing infracture
D. upper management is ultimately responsible for policy implementation PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
Correct Answer: C
QUESTION 129
Which three option are areas of router security?
A. physical security
B. access control list security
C. zone-base firewall security
D. operating system security
E. router hardening
F. cisco IOS-IPS security
Correct Answer: ADE QUESTION 130
You have several operating groups in your enterprise that require different access restrictions to the routers to perform their jobs roles. These groups range from Help Desk personnel to advanced troubleshooters. What is one methodology for controlling access rights to the router in these situation?
A. configure ACLs to control access for these different groups
B. configure multiple privilege level access
C. implement syslogging to monitor the activities of these groups
D. configure TACACS+ to perform scalable authentication
Correct Answer: B QUESTION 131
Which of these is a GUI tool for performing security configuration on Cisco routers?
A. security appliance device manager
B. cisco CLI configuration management tool
C. cisco security device manager
D. cisco security manager
Correct Answer: C QUESTION 132
When implementing network security, what is an important configuration task that you should perform t assist in correlating network and security events?
A. configure network time protocol
B. configure synchronized syslog reporting
C. configure a common repository of all network events for ease of monitoring
D. configure an automated network monitoring system for event correlation PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
Correct Answer: A
QUESTION 133
Which of these options is a Cisco IOS feature that lets you more easily configure security features on your router?
A. cisco self-defending network
B. implementing AAA command authorization
C. the auto secure CLI command
D. performing a security audit via SDM
Correct Answer: C QUESTION 134
Which three of these options are some of the best practices when you implement an effective firewall security policy? (choose three)
A. position firewalls at a strategic inside locations to help mitigate nontechnical attacks
B. configure logging to capture all events for forensic purposes
C. use firewalls as a primary security defense; other security measures and devices shoulde be implemented to enhance your network security
D. position firewalls at key security boundeeries
E. deny all traffic by default and permit only necessary services
Correct Answer: CDE
QUESTION 135
Which option correctly defines asymmetric encryption?
A. uses the same keys to encrypt and decrypt data
B. uses MD5 hashing algorithms for digital signage encryption
C. uses different keys to encrypt and decrypt data
D. uses SHA-1 hashing algorithms for digital signage encryption
Correct Answer: C
QUESTION 136
Which option is a desirable feature of using symmetric encryption algorithms?
A. they are often used for wire-speed encryption in data networks
B. they are based on complex mathematical operations and can easily be accelerated by hardware
C. they offer simple key management properties
D. they are best used for one-time encryption needs
Correct Answer: A
QUESTION 137
Which option is true of using cryptography hashes?
A. they are easily reversed to decipher the message context
B. they convert arbitrary data into fixed length digits
C. they are based on a two-way mathematical function
D. they are used for encrypting bulk data communications
Correct Answer: B
QUESTION 138
Which option is true of intrusion prevention systems?
A. they operate in promiscuous mode
B. they operate in inline mode
C. they have no potential impact on the data segment being monitored
D. they are more vulnerable to evasion techniques than IDS
Correct Answer: B
QUESTION 139
Which statement is true when using zone-based firewalls on a Cisco router?
A. policies are applied to traffic moving between zones, not between interfaces
B. the firewalls can be configured simultaneously on the same interface as classic CBAC using the ip inspect CLI command
C. interface ACLs are applied before zone-based policy firewalls when they are applied outbond
D. when configuring with the ?PASS? action, stateful inspection is applied to all traffic passing between the configured zones
Correct Answer: A
QUESTION 140
From what configuration mode would you enter the set peer ip-address command to specify the IP address of an IPsec peer?
A. Transform set configuration mode
B. Crypto map configuration mode
C. ISAKMP configuration mode
D. Interface configuration mode
Correct Answer: B QUESTION 141
What two site-to-site VPN wizards are available in the Cisco SDM interface? (Choose two.)
A. Easy VPN Setup
B. Quick Setup
C. Step-by-Step
D. DMVPN Setup
Correct Answer: BC QUESTION 142
PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
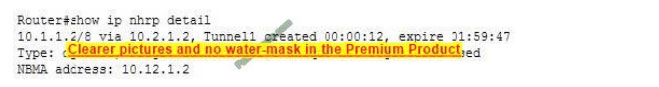
What command displays all existing IPsec security associations (SA)?
A. show crypto isakmp sa
B. show crypto ipsec sa
C. show crypto ike active
D. show crypto sa active
Correct Answer: B QUESTION 143
Which two statements are true about the differences between IDS and IPS? (Choose two.)
A. IPS operates in promiscuous mode.
B. IPS receives a copy of the traffic to be analyzed.
C. IPS operates in inline mode.
D. IDS receives a copy of the traffic to be analyzed.
Correct Answer: CD QUESTION 144
What form of attack are all algorithms susceptible to?
A. Meet-in-the-middle
B. Spoofing
C. Stream cipher
D. Brute-force
Correct Answer: D QUESTION 145
Which type of cipher achieves security by rearranging the letters in a string of text?
A. Stream cipher
B. Transposition cipher
C. Block cipher
Correct Answer: C QUESTION 146
Which of the following are techniques used by symmetric encryption cryptography? (Choose all that apply.)
A. Block ciphers
B. Message Authentication Codes (MAC) PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
C. One-time pad
D. Stream ciphers
Correct Answer: ABD QUESTION 147
DES typically operates in block mode, where it encrypts data in what size blocks?
A. 56-bit blocks
B. 40-bit blocks
C. 128-bit blocks
D. 64-bit blocks
Correct Answer: D QUESTION 148
What method does 3DES use to encrypt plain text?
A. 3DES-EDE
B. EDE-3DES
C. 3DES-AES
D. AES-3DES
Correct Answer: A QUESTION 149
Which of the following is not considered a trustworthy symmetric encryption algorithm?
A. 3DES
B. IDEA
C. EDE
D. AES
Correct Answer: C QUESTION 150
ACE University main campus is located in Santa Cruz. The University has recently established various remote campuses offering e-learning services. The University is using IPsec VPN connectivity between its main and remote campuses San Francisco (SF), South Dakota (SD), Redwood City (RWC). As a recent addition to the IT/Networking team, you have been tasked to document the IPsec VPN configurations to the remote campuses using the Cisco Router and SDM utility. Using the SDM output from VPN Tasks under the Configure tab, answer these questions:
1. Which one of these statements is correct in regards to ACE University IPsec tunnel between its Santa Cruz
PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
main campus and its SF remote campus?
A. It is using IPsec tunnel mode, AES encryption, and SHA HMAC Integrity Check.
B. It is using IPsec transport mode, 3DES encryption, and SHA HMAC Integrity Check.
C. It is using IPsec tunnel mode to protect the traffic between the 10.10.10.0/24 and the 10.2.58.0/24 subnet.
D. It is using digital certificate to authenticate between the IPsec peers and DH group 2.
E. It is using pre-shared key to authenticate between the IPsec peers and DH group 5.
F. The Santa Cruz main campus is the Easy VPN Server and the SF remote campus is the Easy VPN Remote.
Correct Answer: D
QUESTION 151
When using a stateful firewall, which information is stored in the stateful session flow table?
A. the outbound and inbound access rules (ACL entries)
B. the source and destination IP addresses, port numbers, TCP sequencing information, and additional flags for each TCP or UDP connection associated with a particular session
C. all TCP and UDP header information only
D. all TCP SYN packets and the associated return ACK packets only
E. the inside private IP address and the translated inside global IP address
Correct Answer: B
QUESTION 152
Which of these can be used to authenticate the IPsec peers during IKE Phase 1?
A. Diffie-Hellman Nonce
B. pre-shared key
C. XAUTH
D. integrity check value
E. ACS
F. AH
Correct Answer: B
QUESTION 153
What is the primary type of intrusion prevention technology used by the Cisco IPS security appliances?
A. profile-based
B. rule-based
C. signature-based
D. protocol analysis-based
E. netflow anomaly-based
F. Pending
Correct Answer: F
QUESTION 154
When configuring AAA login authentication on Cisco routers, which two authentication methods should be used as the final method administrator can still log in to the router in case the external AAA server fails?
(Choose two.)
A. group RADIUS
B. group TACACS+
C. local PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553
D. krb5
E. enable
F. if-authenticated
G. Pending
Correct Answer: G
QUESTION 155
Which access list will permit HTTP traffic sourced from host 10.1.129.100 port 3030 destined to host 192.168.1.10?
A. access-list 101 permit tcp any eq 303
B. access-list 101 permit tcp 10.1.128.00.0.1.255 eq 3030 192.168.1.00.0.0.15 eq www
C. access-list 101 permit tcp 10.1.129.00.0.0.255 eq www 192.168.1.100.0.0.0 eq www
D. access-list 101 permit tcp host 192.168.1.10 eq 80 10.1.0.00.0.255.255 ep 3030
E. access-list 101 permit tcp 192.168.1.100.0.0.0 eq 80 10.1.0.00.0.255.255
F. access-list 101 permit ip host 10.1.129.100 eq 3030 host 192.168.1.100 eq 80
Correct Answer: B
QUESTION 156
Which characteristic is the foundation of Cisco Self-Defending Network technology?
A. secure connectivity
B. threat control and containment
C. policy management
D. secure network platform
Correct Answer: D
QUESTION 157
Which Cisco IOS command is used to verify that either the Cisco IOS image, the configuration files, or both have been property backed?
A. show archive
B. show secure bootset
C. show flash
D. show file systems
E. dir
F. dir archive
Correct Answer: B
QUESTION 158
Which aaa accounting command is used to enable logging of both the stat and stop records for user terminal
PassGuide.com-Make You Succeed To Pass IT Exams PassGuide 640-553 sessions on the router?
A. aaa accounting network start-stop tacacs+
B. aaa accounting system start-stop tacacs+
C. aaa accounting exec start-stop tacacs+
D. aaa accounting connection start-stop tacacs+
E. aaa accounting commands 15 start-stop tacacs+
Correct Answer: C
QUESTION 159
What does the MD5 algorithm do?
A. takes a message less than 2^64 bits as input and produces a 160-bit message digest
B. takes a variable-length message and produces a 168-bit message digest
C. takes a variable-length message and produces a 128-bit message digest
D. takes a fixed-length message and produces a 128-bit message digest
E. Pending
Correct Answer: E
QUESTION 160
Which statement is true about asymmetric encryption algorithms?
A. They use the same key for encryption and decryption of data.
B. They use the same key for decryption but different keys for encryption of data.
C. They use different keys for encryption and decryption of data.
D. They use different keys for decryption but the same key for encryption of data.
Correct Answer: C
Qualifying for the Cisco 640-553 exam sample questions means that, you have accomplished something big in your IT profession which can help you reach new pinnacles of success. Here are some fantastic suggestions for the learners planning for the Cisco 640-553 certification assessment. You can go through these points properly so they can improve your upcoming profession in the IT industry. First of all, to be able to understand about the subjects associated with this assessment, you need to study the latest Cisco 640-553 exam sample questions HP places designed by various IT experts. These places involve each and every thing associated with the Cisco 640-553 exam sample questions like the concerns which can be appearing in the assessment.
Welcome to download the newest Pass4itsure 2V0-641 dumps: https://www.pass4itsure.com/2v0-641.html
http://www.maeeonline.org/gaqm-csm-001-pdf-first-hand-gaqm-csm-001-vce-pdf-covers-all-key-points/