Understanding the basic concepts of the Cisco 350-901 exam does not mean that you will easily pass the Cisco Certification 350-901 exam. Some preparation is required to get through 350-901. With the help of available 350-901 dumps training resources, it’s a good idea to gain hands-on experience and practice on the 350-901 itself.
This exam 350-901 is not difficult to pass. With the help of 350-901 dumps practice questions, the exam is easy. The Pass4itSure 350-901 exam dumps ( visit: https://www.pass4itsure.com/350-901.html Get the complete Cisco 350-901 exam dumps. ) have been updated with all exam questions and answers to verify the authenticity and validity.
The latest Cisco 350-901 exam practice questions (parts) are shared below, from Pass4itSure 350-901 dumps
Up-to-date Cisco 350-901 exam dumps PDF free
Cisco 350-901 dumps pdf https://drive.google.com/file/d/1jfTryr67cwI6DuBCRhjoA7KbPSA_D-mK/view?usp=sharing
Share some online Cisco 350-901 tests (Increase your knowledge)
QUESTION 1 #
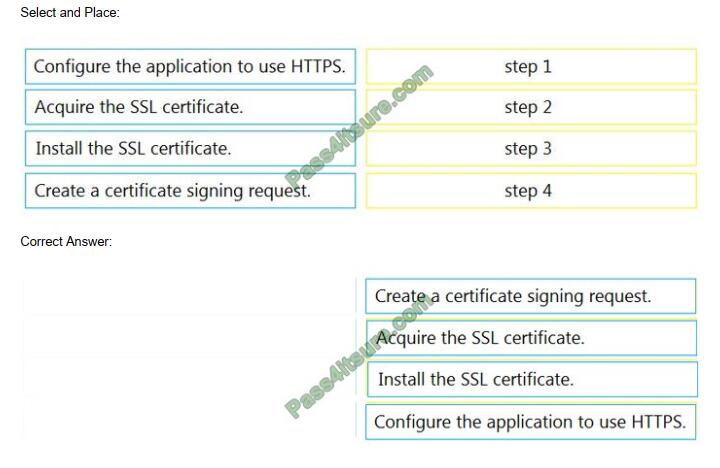
DRAG-DROP
An engineer is developing a web-based application that will be used as a central repository for the HR department. The
application needs to authenticate user access and encrypt communication. Drag and drop the steps from the left into the order on the right to install an application-specific SSL certificate.
QUESTION 2 #
FILL BLANK
A local Docker image has an image ID of 386231131. Fill in the blanks to complete the command in order to tag the
image into the “cisco” repository with “version1 0\\'”.

Correct Answer: See below
$docker tag 386231131 cisco/386231131:version1.0
QUESTION 3 #
What is the benefit of continuous testing?
A. increases the number of bugs found in production
B. enables parallel testing
C. removes the requirement for test environments
D. decreases the frequency of code check-ins
Correct Answer: B
QUESTION 4 #
A heterogeneous network of vendors and device types needs automating for better efficiency and to enable future
automated testing. The network consists of switches, routers, firewalls, and load balancers from different vendors,
however, they all support the NETCONF/RESTCONF configuration standards and the YAML models with every feature
the business requires.
The business is looking for a buy versus build solution because they cannot dedicate engineering
resources and they need configuration diff and rollback functionality from day 1.
Which configuration management for automation tooling is needed for this solution?
A. Ansible
B. Ansible and Terraform
C. NSO
D. Terraform
E. Ansible and NSO
Correct Answer: C
QUESTION 5 #
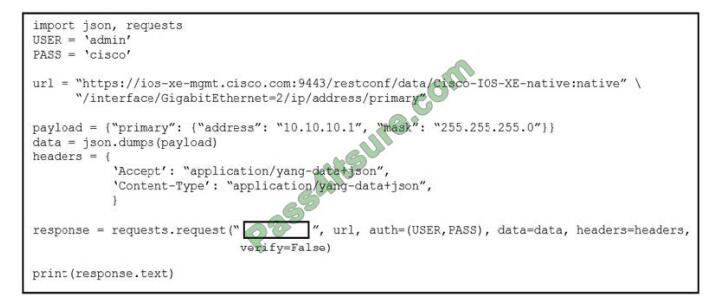
Refer to the exhibit. Which RESTCONF verb changes the GigabitEthernet2 interface from 192.168.100.1/24 to
10.10.10.1/24?
A. POST
B. PATCH
C. GET
D. HEAD
Correct Answer: A
Reference: https://blogs.cisco.com/developer/python-scripting-apis
QUESTION 6 #
Which two types of storage are supported for app hosting on a Cisco Catalyst 9000 Series Switch? (Choose two.)
A. external USB storage
B. internal SSD
C. CD-ROM
D. SD-card
E. bootflash
Correct Answer: AB
QUESTION 7 #
An organization manages a large cloud-deployed application that employs a microservices architecture. No notable issues occur with downtime because the services of this application are redundantly deployed over three or more data
center regions.
However, several times a week reports are received about application slowness. The container
orchestration logs show faults in a variety of containers that cause them to fail and then spin up brand new.
Which action must be taken to improve the resiliency design of the application while maintaining the current scale?
A. Update the base image of the containers.
B. Test the execution of the application with another cloud services platform.
C. Increase the number of containers running per service.
D. Add consistent “try/catch(exception)” clauses to the code.
Correct Answer: D
QUESTION 8 #
Which Puppet manifest needs to be used to configure an interface GigabitEthernet 0/1 on a Cisco IOS switch?
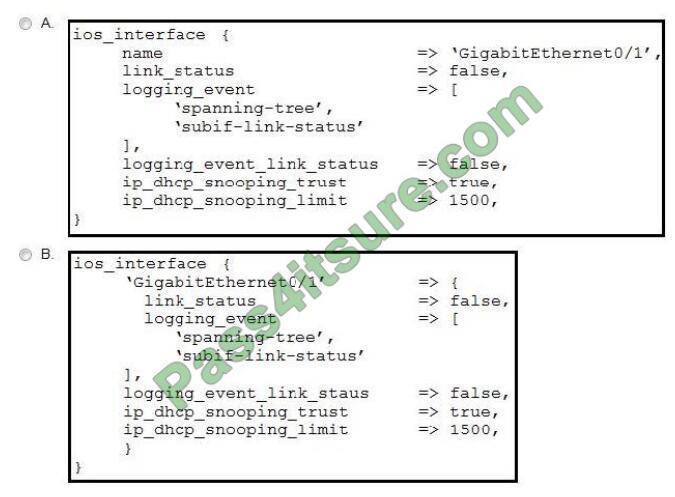
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: D
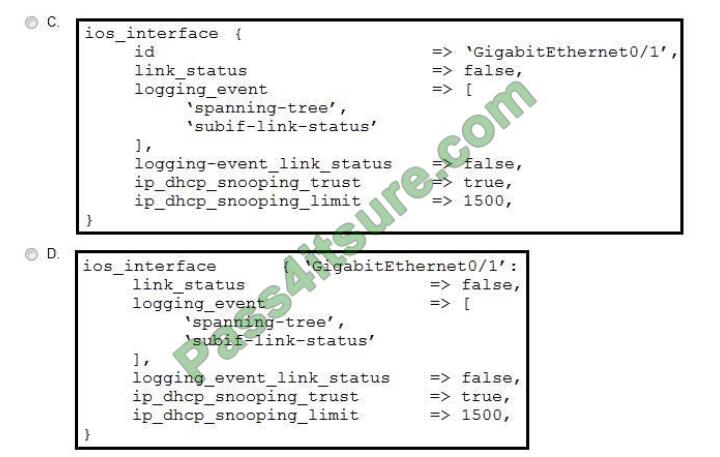
QUESTION 9 #
Refer to the exhibit. What is the missing step in deploying a Docker container to IOx?
A. Build the package.YAML file.
B. Pull/push the image to the Docker registry.
C. Build the package. cert file to sign the app.
D. Log in to Device Manager.
Correct Answer: A
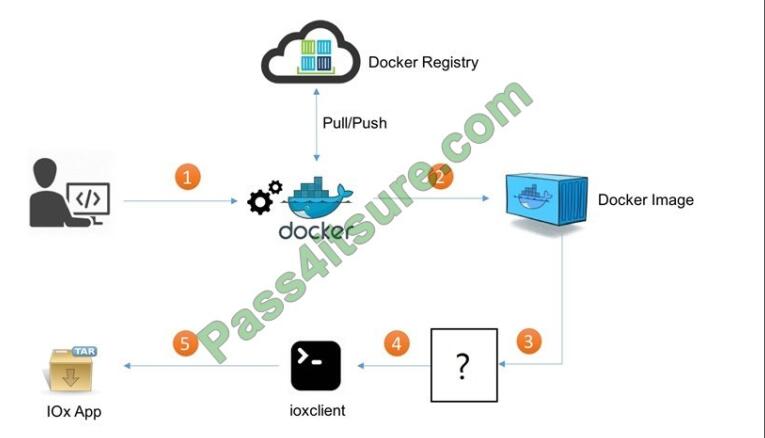
QUESTION 10 #
DRAG DROP An engineer must access multiple bots that are running in internal infrastructure. A different HTTPS
URL is required for each bot. The infrastructure has just one public IP address and a Linux server with Apache installed.
Drag and drop the actions from the left into the order of steps on the right to enable access to the bots inside. Not all
options are used.
Select and Place:
QUESTION 11 #
Why is end-to-end encryption deployed when exposing sensitive data through APIs?
A. Data transfers are untraceable from source to destination.
B. Data cannot be read or modified other than by the true source and destination.
C. Server-side encryption enables the destination to control data protection.
D. Traffic is encrypted and decrypted at every hop in the network path.
Correct Answer: D
QUESTION 12 #
What is a characteristic of monolithic architecture?
A. It is an application with multiple independent parts.
B. New capabilities are deployed by restarting a component of the application.
C. A service failure can bring down the whole application.
D. The components are platform-agnostic.
Correct Answer: C
QUESTION 13 #
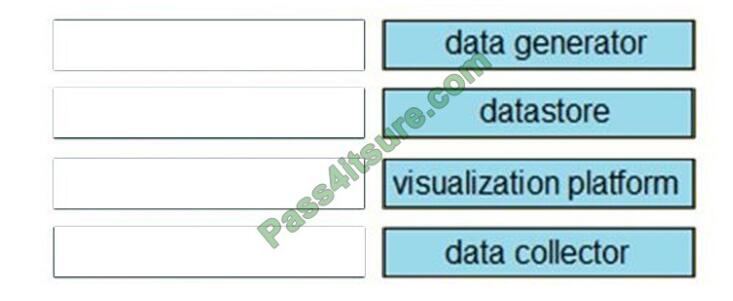
DRAG-DROP
A Python application is being written to run inside a Cisco IOS XE device to assist with gathering telemetry data. Drag
and drop the elements of the stack from the left onto the functions on the right to collect and display the telemetry
streaming data.
Select and Place:
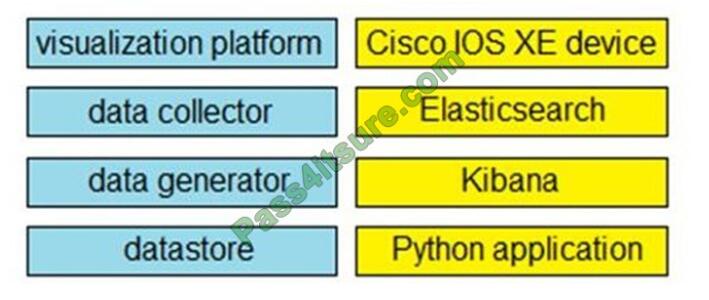
Correct Answer:
Finally,
You can’t pass the 350-901 exam just by knowing the basic concepts of the exam. You need to use the power of 350-901 dump to practice daily. Get the complete 350-901 dumps here: https://www.pass4itsure.com/350-901.html Q&As: 199.
Pass4itSure is a leader in the exam certification industry and enjoys high popularity. 100% help you pass the exam smoothly. Remember, the first completion does not guarantee that you will pass the score, but the correct answer to the question. wish you all the best!