How 300-915 DEVIOT dumps help to pass Cisco 300-915 exam
Even if it is a general exam, it is not possible to pass the exam through the simplified information of the content of the syllabus. Not to mention the Cisco 300-915 exam is not simple. This is the easiest way to get through, guiding you to your final destination with excellent 300-915 deviot dumps.

With Pass4itSure’s high-quality 300-915 deviot dumps >>>https://www.pass4itsure.com/300-915.html (300-915 DEVIOT Dumps PDF + VCE), passing the Cisco 300-915 exam has never been easier.
Latest Cisco 300-915 braindumps [2021] : PDF dumps – Pass exam with ease
Google Drive: Cisco 300-915 pdf free https://drive.google.com/file/d/1_lDLj7feW2fYtchGkg324eQG3TotFy_W/view?usp=sharing
New Cisco 300-915 practice exam – practice test questions answers
QUESTION 1 #
A network is being configured for an Ethernet-connected sensor. The sensor fails to send data to the configured
destination. The IP address of the sensor can be pinged from a laptop on the same subnet. When a different subnet is
used, the sensor cannot be reached, but other clients on the same subnet are still accessible.
What are two reasons for the connectivity problem? (Choose two.)
A. wrong DNS server on the sensor
B. wrong subnet mask on your laptop
C. wrong default gateway on the sensor
D. wrong default gateway on your laptop
E. wrong subnet mask on the sensor
Correct Answer: CE
QUESTION 2 #
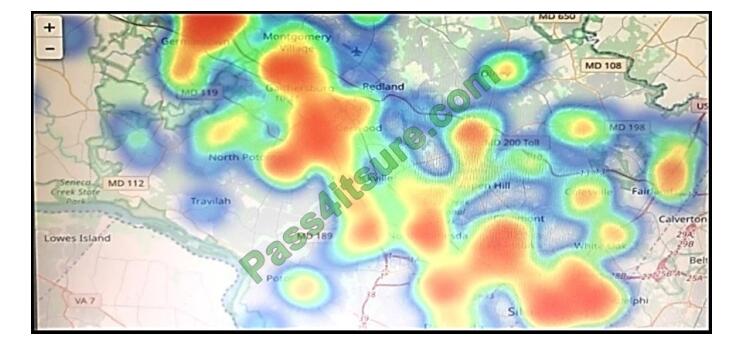
Refer to the exhibit. Which two statements are true? (Choose two.)
A. That is a heatmap projected on top of a geographic map.
B. That is a treemap projected on top of a geographic map.
C. The color red usually stands for lower values and the color blue usually stands for higher values.
D. Another suitable visualization technique for this image would be line graphs.
E. The color blue usually stands for lower values and the color red usually stands for higher values.
Correct Answer: AE
QUESTION 3 #
How do the Cisco router (IR) and switch (IE) portfolio support edge data services?
A. Edge data services can be run and managed as containers using Cisco IOx.
B. Edge data services can run only in virtual machines on a separate compute layer.
C. Edge data services are aliases for IR/IE configuration services.
D. Edge data services run as separate instances only on virtual machines.
Correct Answer: C
QUESTION 4 #
Which connector is southbound?
A. horizontal connector
B. cloud connector
C. device connector
D. universal connector
Correct Answer: C
QUESTION 5 #
Which two data sources are used with a visualization tool such as Grafana? (Choose two.)
A. Microsoft Power BI
B. Kibana
C. InfluxDB
D. Elasticsearch
E. Tableau
Correct Answer: CD
QUESTION 6 #
Which command is used to package a Docker-style Cisco IOx app using ioxclient?
A. ioxclient docker create helloworld:1.0.
B. ioxclient docker-app helloworld:1.0.
C. ioxclient docker package helloworld:1.0.
D. ioxclient docker helloworld:1.0.
Correct Answer: C
QUESTION 7 #
Mosquitto was installed correctly on the Cisco IR829 router like a Cisco IOx application. When the sensor is connected to the broker on the Cisco IR829 router with the default port, the connection is refused (Error Code 5).
Which action should be done to resolve the issue?
A. Insert in the IOS config: IP nat inside source static TCP 1883 interface GigabitEthernet0 1883
B. Insert in the package_config.ini file under section ports: TCP: [“8883”]
C. Use the correct username and password.
D. Insert in the package.YAML file under section ports: TCP: [“1883”]
Correct Answer: C
QUESTION 8 #
DRAG-DROP
The network team of a large international airport is creating a sensor network on their site using the Cisco LoRaWAN
solution. Drag and drop the actions from the left to right needed to implement this project. Not all options are used.
Select and Place:
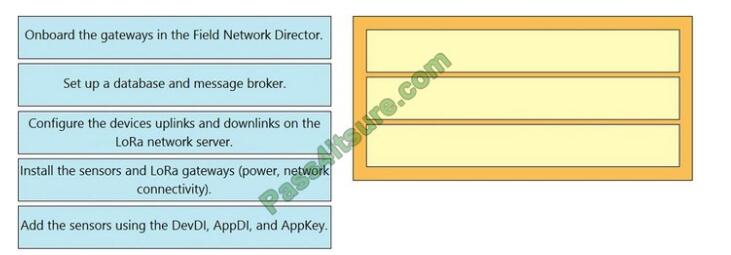
Correct Answer:
Reference: https://www.cisco.com/c/en_in/solutions/internet-of-things/lorawan-solution.html#~stickynav=3
QUESTION 9 #
As part of an IoT project, an organization is developing an application that will share multiple clients using a REST API.
Based on the software development process, what are two valid technical activities that can be suggested to secure the
REST API that is developed during the development of the software? (Choose two.)
A. Respond to request failures in detail to allow users for easier troubleshooting.
B. Implement HTTP whitelisting to only methods that are allowed.
C. Implement and review audit logs for security-related events.
D. Reject HTTP methods that are invalid with an error code 404.
E. Implement physical firewalling and access control to the resources.
Correct Answer: BD
QUESTION 10 #
Which data visualization technique should be used to represent an important single metric on a dashboard?
A. heatmap
B. scatter pot
C. gauge
D. treemap
Correct Answer: C
QUESTION 11 #
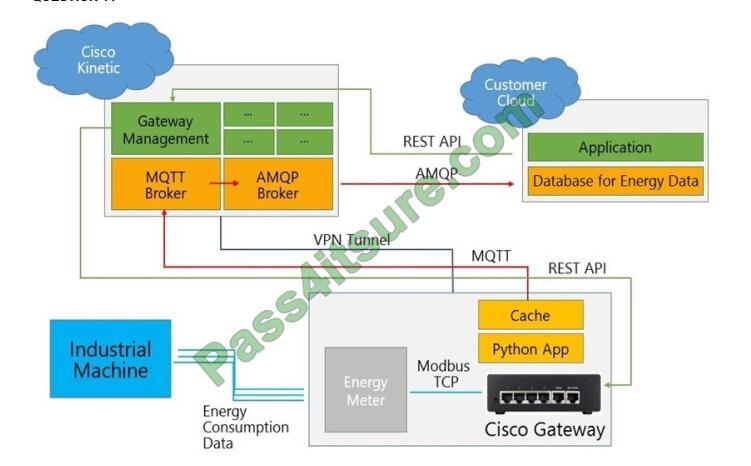
Refer to the exhibit. Which two statements about data flow are true? (Choose two.)
A. Another AMQP broker should be implemented on the customer cloud.
B. Instead of AMQP, MQTT should be used for compatibility issues in a cloud-to-cloud connection.
C. A VPN tunnel is not necessary because the MQTT payload is encrypted by default.
D. The gateway must stay constantly connected to the Kinetic cloud to avoid blank data sets, even when using caching
functions.
E. The Python application could use the paho-mqtt library.
Correct Answer: BE
QUESTION 12 #
What are the two functionalities of edge data services? (Choose two.)
A. creating a machine learning data model
B. supporting many interfaces and APIs
C. applying advanced data analytics
D. filtering, normalizing and aggregating data
E. saving data for a prolonged time period
Correct Answer: DE
QUESTION 13 #
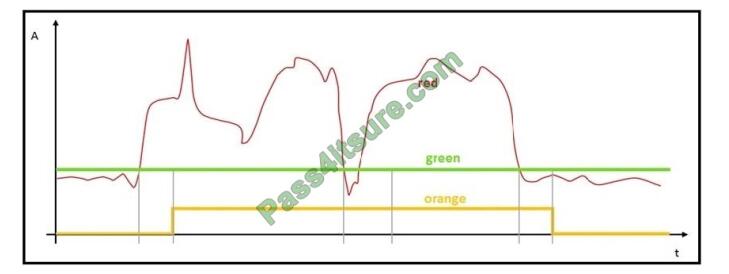
Refer to the exhibit. The graph has been provided by the monitoring team to the IoT Engineer. The red line represents
the consumption of energy from an industrial machine.
Which two pieces of information can be captured? (Choose two.)
A. The green graph visualizes the mean value of the data points.
B. The green graph visualizes if the electronic device is not in standby mode.
C. The orange graph visualizes a boolean: power on/off.
D. The orange graph contains more information than the red graph.
Correct Answer: AC
QUESTION 14 #
An IoT engineer is responsible for security at an organization. Humans and machines need to be allowed to access
services like databases or computing on AWS. The engineer decides to implement dynamic secrets.
Which method helps to get this implementation accurate from a security point of view?
A. Create a central secret system for humans and machines to obtain very short-lived dynamic secrets to access any
service.
B. Humans cannot be trusted, and each time they authenticate they should be issued with dynamic secrets. Machines
can be trusted, and they can be issued with static credentials.
C. Maintain a different service associated with secret systems to issue access.
D. After a user is authenticated by any trusted system, the user can be trusted to use any service.
Correct Answer: A
QUESTION 15 #
A sensor reads potentially critical data from an industrial device, but most of the data from the sensor is not critical
information and does not change unless a critical event happens.
Which data workflow is appropriate for how the critical and non-critical data is processed?
A. 1. Acquire sensor data.
2. Filter non-actionable data.
3. Perform action on data.
4. Send critical data and action performed on data to the cloud for storing.
B. 1. Acquire sensor data.
2. Send data to the cloud for processing and to determine action.
3. Send required action back to edge for action completion.
4. Perform action on data.
C. 1. Acquire sensor data.
2. Filter non-actionable data.
3. Perform action on data.
D. 1. Acquire sensor data.
2. Perform action on data.
3. Send data and action performed on data to the cloud for recording.
Correct Answer: D
It’s hard to imagine cisco 300-915 exams with such good offers. However, for 300-915 deviot dumps, this is a daytime reality. It will help you pass the exam easily.
Best 300-915 deviot dumps >>> https://www.pass4itsure.com/300-915.html Although the Developing Solutions using Cisco IoT and Edge Platforms (DEVIOT) 300-915 exam is the hardest to crack, with it, easy to pass, you just need to learn the basics and practice the 300-915 deviot dumps exam questions.