Welcome to download the newest Pass4itsure 117-201 VCE dumps: http://www.pass4itsure.com/117-201.html
At Flydumps,we are positive that our CheckPoint 156-215 exam preparation material with questions and answers pdf provide most in-depth solutions for individuals that are preparing for the CheckPoint 156-215 exam.Our uodated CheckPoint 156-215 exam dumps will allow you the opportunity to know exactly what to expect on the exam day and ensure that you can pass the exam beyond any doubt.
QUESTION 95
You are a security consultant for a hospital. You are asked to create some type of authentication rule on the NGX Security Gateway, to allow doctors to update patients’ records via HTTP from various workstations. Which authentication method should you use?
A. Client Authentication
B. LDAP Authentication
C. SecureID Authentication
D. TACAS Authentication
E. User Authentication
Correct Answer: E
QUESTION 96
Your Rule Base includes a Client Authentication rule, with partial authentication and standard sign on for HTTP, Telnet, and FTP services. The rule was working, until this morning. Now users are not prompted for authentication, and they see error “page cannot be displayed” in the browser. In SmartView Tracker, you discover the HTTP connection is dropped when the Gateway is the destination. What caused Client Authentication to fail?
A. You added a rule below the Client Authentication rule, blocking HTTP from the internal network.
B. You disabled NGX Control Connections in Global Properties.
C. The browsers’ proxy settings have changed.
D. You enabled Static NAT on the problematic machines.
E. You added the Stealth Rule before the Client Authentication rule.
Correct Answer: E
QUESTION 97
You have just started a new job as the Security Administrator for Widgets Inc. Your boss has asked you to ensure that peer-to-peer file sharing is not allowed past the corporate Security Gateway. Where should you configure this?
A. SmartDashboard > SmartDefense
B. SmartDashboard > WebDefense
C. By editing the file $FWDIR/conf/application_intelligence.C
D. SmartDashboard > Policy > Global Properties > Malicious Activity Detection
E. SmartDashboard > Web Intelligence
Correct Answer: A
QUESTION 98
Ivan’s main internal network 10.10.10.0/24 allows all traffic to the Internet using Hide NAT. Ivan also has a small network 10.10.20.0/24 behind the internal router. Ivan wants to configure the kernel to translate the source address only when network 10.10.20.0 tries to access the Internet for HTTP, SMTP, and FTP services.
Which of the following configurations will allow this network to access Internet?
A. Automatic Static NAT on network 10.10.20.0/24
B. Manual Hide NAT rules for HTTP, FTP, and SMTP services for network 10.10.20.0/24
C. Manual Static NAT rules for network 10.10.20.0/24
D. Automatic Hide NAT for network 10.10.20.0/24
E. No change is necessary
Correct Answer: B
QUESTION 99
What does schema checking do?
A. Authenticates users attempting to access resources protected by an NGX Security Gateway.
B. Verifies that every object class, and its associated attributes, is defined in the directory schema.
C. Maps LDAP objects to objects in the NGX objects_5_0.C file.
D. Verifies the Certificate Revocation List for Certificate validity.
E. Provides topology downloads for SecuRemote and SecureClient users authenticated by an LDAP server.
Correct Answer: B
QUESTION 100
You have blocked an IP address via the Block Intruder feature of SmartView Tracker. How can you see the addresses you have blocked?
A. In SmartView Status click the Blocked Intruder tab.
B. Run fwm blocked_view.
C. Runfw sam a.
D. Run fw tab sam_blocked_ips.
E. In SmartView Tracker, click the Active tab, and the actively blocked connections display.
Correct Answer: D
QUESTION 101
After importing the NGX schema into an LDAP server, what should you enable?
A. Schema checking
B. Encryption
C. UserAuthority
D. ConnectControl
E. Secure Internal Communications
Correct Answer: A
QUESTION 102
You create two Policy Packages for two NGX Security Gateways. For the first Policy Package, you selected Security and Address Translation and QoS Policy. For the second Policy Package, you selected Security and Address Translation and Desktop Security Policy. In the first Policy Package, you enabled host-based port scan from the SmartDefense tab. You save and install the policy to the relevant Gateway object. How is the port scan configured on the second Policy Package’s SmartDefense tab?
A. Host-based port scan is disabled by default.
B. Host-based port scan is enabled, because SmartDefense settings are global.
C. Host-based port scan is enabled but it is not highlighted.
D. There is no SmartDefense tab in the second Policy Package.
Correct Answer: B
QUESTION 103
Your primary SmartCenter Server runs on SecurePlatform. What is the easiest way to back up your NGX configuration, including routing and network configuration files?
A. Using the upgrade_export command in the $FWDIR\bin directory
B. Running a conf_merge with an objects_5_0.C from a new NGX installation
C. Copying the contents of $FWDIR to another location
D. Copying the $FWDIR\conf and $FWDIR\lib directory to another location
E. Using the native SecurePlatform backup utility from command line or in Web based interface
Correct Answer: E QUESTION 104
When you find a suspicious connection from a problematic host, you want to block everything from that whole network, not just the host. You want to block this for an hour, but you do not want to add any rules to the Rule Base. How do you achieve this?
A. Create a Suspicious Activity rule in SmartView Tracker.
B. Create a Suspicious Activity Rule in SmartView.
C. Create an “FW SAM” rule in SmartView Monitor.
D. Select “block intruder” from the Tools menu in the SmartView Tracker.
Correct Answer: B QUESTION 105
William is a Security Administrator who has added address translation for his internal Web server to be accessible by external clients. Due to poor network design by his predecessor, William sets up manual NAT rules for this server, while his FTP server and SMTP server are both using automatic NAT rules. All traffic from his FTP and SMTP servers are passing through the Security Gateway without a problem, but traffic from the Web server is dropped because of anti-spoofing settings. What is causing this?
A. “Allow bi-directional NAT” is not checked in Global Properties.
B. “Translate destination on client side” is not checked in Global Properties under “Manual NAT Rules”.
C. “Translate destination on client side” is not checked in Global Properties > Automatic NAT Rules”.
D. Routing is not configured correctly.
E. Manual NAT rules are not configured correctly.
Correct Answer: B QUESTION 106
Jack’s project is to define the backup and restore section of his organization’s disaster recovery plan for his
organization’s distributed NGX installation. Jack must meet the following required and desired objectives:
Required Objective: The security policy repository must be backed up no less frequently than every 24
hours.
Desired Objective: The NGX components that enforce the Security Policies should be backed up no less
frequently than once a week.
Desired Objective: Back up NGX logs no less frequently than once a week. Administrators should be able
to view backed up logs in SmartView Tracker.
Jack’s disaster recovery plan is as follows:
Use the cron utility to run the upgrade_export command each night on the SmartCenter Servers.
Configure the organization’s routine backup software to back up the files created by the upgrade_export
command.
Configure the SecurePlatform backup utility to back up the Security Gateways every Saturday night.
Use the cron utility to run the upgrade_export command each Saturday night on the Log Servers.
Configure an automatic, nightly logexport. Configure the organization’s routine backup software to back up
the exported logs every night.
Jack’s plan:
A. Meets the required objective but does not meet either desired objective
B. Meets the required objective and both desired objectives
C. Meets the required objective and only one desired objective
D. Does not meet the required objective
Correct Answer: C
QUESTION 107
Thomas is the Security Administrator for an online bookstore. Customers connect to a variety of Web servers to place orders, change orders, and check the status of their orders.
Thomas checked every box in the Web Intelligence tab, and installed the Security Policy. He ran penetration test through the Security Gateway, to determine if the Web servers were protected from cross-site scripting attacks. The penetration testing indicated the Web servers were still vulnerable.
Which of the following might correct the problem?
A. The penetration software Thomas is using is malfunctioning and is reporting a false-positive.
B. Thomas must create resource objects, and use them in the rules allowing HTTP traffic to the Web servers.
C. Thomas needs to check the “Products > Web Server” box on the host node objects representing his Web servers.
D. Thomas needs to check the “Web Intelligence” box in the SmartDefense > HTTP properties.
E. Thomas needs to configure the Security Gateway protecting the Web servers as a Web server.
Correct Answer: C
QUESTION 108
You are a Security Administrator configuring Static NAT on an internal host-node object. You clear the box “Translate destination on client site”, accessed from Global Properties > NAT settings > Automatic NAT. Assuming all other Global Properties NAT settings are selected, what else must be configured for automatic Static NAT to work?
A. The NAT IP address must be added to the anti-spoofing group of the external Gateway interface
B. Two address-translation rules in the Rule Base
C. No extra configuration needed
D. A proxy ARP entry, to ensure packets destined for the public IP address will reach the Security Gateway’s external interface
E. A static route, to ensure packets destined for the public NAT IP address will reach the Gateway’s internal interface
Correct Answer: E
QUESTION 109
Jill is about to test some rule and object changes suggested in an NGX newsgroup. Which backup and restore solution should Jill use, to ensure she can most easily restore her Security Policy to its previous configuration, after testing the changes?
A. SecurePlatform backup utilities
B. Manual copies of the $FWDIR/conf directory
C. upgrade_export and upgrade_import commands
D. Policy Package management
E. Database Revision Control
Correct Answer: E
QUESTION 110
Select the correct statement about Secure Internal Communications (SIC) Certificates? SIC Certificates: A. for NGX Security Gateways are created during the SmartCenter Server installation.
B. for the SmartCenter Server are created during the SmartCenter Server installation.
C. are used for securing internal network communications between the SmartView Tracker and an OPSEC device.
D. decrease network security by securing administrative communication among the SmartCenter Servers and the Security Gateway.
E. uniquely identify Check Point enabled machines; they have the same function as Authentication Certificates.
Correct Answer: B
QUESTION 111
Review the following rules and note the Client Authentication Action properties screen, as shown in the exhibit:
After being authenticated by the Security Gateway, when a user starts an HTTP connection to a Web site, the user tries to FTP to another site using the command line. What happens to the user? The:
A. FTP session is dropped by the implicit Cleanup Rule.
B. user is prompted from that FTP site only, and does not need to enter username and password for Client Authentication.
C. FTP connection is dropped by rule 2.
D. FTP data connection is dropped, after the user is authenticated successfully.
E. user is prompted for authentication by the Security Gateway again.
Correct Answer: B
QUESTION 112
Which NGX configuration setting forces the Client Authentication authorization time-out to refresh, each time a new user is authenticated? Choose ONE. The:
A. “Time” properties, adjusted on the user objects for each user, in the source of the Client Authentication rule
B. Time object, with hours restricted and renewable, in the Time field of the Client Authentication rule
C. SmartDefense > Application Intelligence > Client Authentication > Refresh User Timeout option enabled
D. Global Properties > Authentication parameters, adjusted to allow for “Regular Client Refreshment”
E. “Refreshable Timeout” setting, in the Limit tab of the Client Authentication Action properties screen
Correct Answer: E
QUESTION 113
How are cached usernames and passwords cleared from the memory of an NGX Security Gateway?
A. Usernames and passwords only clear from memory after they time out.
B. By retrieving LDAP user information, using the fw fetchldap command
C. By using the Clear User Cache button in SmartDashboard
D. By installing a Security Policy
E. By pushing new user information from the LDAP server
Correct Answer: D
QUESTION 114
A digital signature:
A. Uniquely encodes the receiver of the key.
B. Provides a secure key exchange mechanism over the Internet.
C. Guarantees the authenticity and integrity of a message.
D. Automatically changes shared keys.
E. Decrypts data to its original form.
Correct Answer: C
QUESTION 115
Diffie-Hellman uses which type of key exchange?
A. Adaptive
B. Asymmetric
C. Symmetric
D. Static
E. Dynamic
Correct Answer: B
QUESTION 116
Amy is configuring a User Authentication rule for the technical-support department to access an intranet server. What is the correct statement?
A. The Security Server first checks if there is any rule that does not require authentication for this type of connection.
B. The User Authentication rule must be placed above the Stealth Rule.
C. Once a user is first authenticated, the user will not be prompted for authentication again until logging out.
D. Amy can only use the rule for Telnet, FTP, and rlogin services.
E. Amy can limit the authentication attempts in the Authentication tab of the User Properties screen.
Correct Answer: A
QUESTION 117
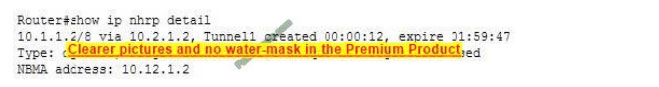
What is the reason for the Critical Problem notification in this SmartView Monitor example?
A. Active real memory shortage on the Gateway
B. No Security Policy installed on the Security Gateway
C. Version mismatch between the SmartCenter Server and Security Gateway
D. Time not synchronized between the SmartCenter Server and Security Gateway
E. No Secure Internal Communications established between the SmartCenter Server and Security Gateway
Correct Answer: B
QUESTION 118
You are setting up a Virtual Private Network, and must select an encryption scheme. Your data is extremely business sensitive and you want maximum security for your data communications. Which encryption scheme would you select?
A. Tunneling mode encryption
B. In-place encryption
C. Either one will work without compromising performance
Correct Answer: A
QUESTION 119
There is a Web server behind your perimeter Security Gateway. You need to protect the server from network attackers, who create scripts that force your Web server to send user credentials or identities to other Web servers. Which box do you check in the SmartDashboard Web Intelligence tab?
A. HTTP protocol inspection protection
B. Cross Site Scripting protection
C. HTTP header format checking
D. Command Injection protection
E. SQL Injection protection
Correct Answer: B
QUESTION 120
Ilse manages a distributed NGX installation for a large bank. Ilse needs to know which Security Gateways have licenses that will expire within the next 30 days. Which SmartConsole application should Ilse use to gather this information?
A. SmartView Monitor
B. SmartUpdate
C. SmartDashboard
D. SmartView Tracker
E. SmartView Status
Correct Answer: B
QUESTION 121
A user attempts authentication using SecureClient. The user’s password is rejected, even though it is correctly defined in the LDAP directory. Which of the following is a valid cause?
A. The LDAP server has insufficient memory.
B. The LDAP and Security Gateway databases are not synchronized.
C. The SmartCenter Server cannot communicate with the LDAP server.
D. The user has defined the wrong encryption scheme.
E. The user is defined in both the NGX user database and the LDAP directory.
Correct Answer: E
QUESTION 122
You create implicit and explicit rules for the following network. The group object “internal-networks”
includes networks 10.10.10.0 and 10.10.20.0. Assume “Accept ICMP
requests” is enabled as before last in the Global Properties.Based on these rules, what happens if you
Ping from host 10.10.10.5 to a host on the Internet, by IP address? ICMP will be:
A. dropped by rule 0.
B. dropped by rule 2, the Cleanup Rule.
C. accepted by rule 1.
D. dropped by the last implicit rule.
E. accepted by the implicit rule.
Correct Answer: C
QUESTION 123
Using SmartDefense how do you notify the Security Administrator that malware is scanning specific ports? By enabling:
A. Network Port scan
B. Host Port Scan
C. Malware Scan protection
D. Sweep Scan protection
E. Malicious Code Protector
Correct Answer: D
QUESTION 124
How many administrators can be created during installation of the SmartCenter Server?
A. Only one
B. Only one with full access and one with read-only access
C. As many as you want
D. Depends on the license installed on the Smart Center Server
E. Specified in the Global Properties
Correct Answer: A
QUESTION 125
Which ldif file must you modify to extend the schema of a Windows 2000 domain?
A. In NGX you do not need to modify any .ldif file
B. The appropriate .ldif file is located in the Security Gateway: $FWDIR/conf/ldif/Microsoft_ad_schema.ldif
C. The appropriate .ldif file is located in the SmartCenter Server: $FWDIR/lib/ldap/ schema_microsoft_ad.ldif
D. The appropriate .ldif file is located in the Security Gateway: $FWDIR/lib/ldif/Microsoft_ad_schema.ldif
E. The appropriate .ldif file is located in the SmartCenter Server: $FWDIR/conf/ldif/ Microsoft_ad_schema.ldif
Correct Answer: C
If you prepare for the CheckPoint 156-215 exam using our FLYDUMPS CheckPoint 156-215 practice test, we guarantee your success in the first attempt. FLYDUMPS fully loaded questions and CheckPoint 156-215 real exam are the absolute perfect and preferred method of preparing for the CheckPoint 156-215 exams by thousands of successful certified professionals across the globe. The answers in the FLYDUMPS CheckPoint 156-215 practice test are written in detail to explain each and every point and completely answers that can come in your final exam. All you will need to do is send us proof of your failing grade, and fill out a special form that we will give you.
Pass4itsure 117-201 dumps with PDF + Premium VCE + VCE Simulator: http://www.pass4itsure.com/117-201.html