Welcome to download the newest Examwind 220-010 dumps:
The 100% valid Flydumps latest Checkpoint 156-915 question answers ensure you 100% pass! And now we are offering the free new version along with the VCE format Checkpoint 156-915 practice test. Free download Checkpoint 156-915 more new PDF and VCE on Flydumps.com.
QUESTION 160
A user accesses the user portal using Integrity Secure Workspace, and attempts to initialize a network application using SSL Network Extender. The application fails to start. What is the MOST
67 LIKELY solution?
A. Select the option Auto-detect client capabilities
B. Select the option Enable SSL Network Extender Application Mode only
C. Select the option Turn off all SSL tunneling clients
D. Select the option Enable SSL Network Extender Network Mode only
Correct Answer: B QUESTION 161
While using the SmartProvisioning to create a new profile, you cannot continue because there are no devices to select. What is the possible reason for this? i) All devices already have a profile assigned to them ii) Provisioning Blade is not enabled on the devices iii) No UTM- 1/Power- 1/Secure Platform devices are defined in SmartDashboard iv) SIC is not established on the devices.
A. ii, iii, iv
B. ii only
C. iii, and iv
D. i, iii
Correct Answer: B QUESTION 162
What is a task of the IPS Event Analysis Server?
A. Invoke defined automatic reactions
B. Display the received events
C. Analyze each IPS log entry as it enters the Log server
D. Add events to the events database
Correct Answer: C QUESTION 163
Message digests use which of the following?
A. SHA-1 and MD5
B. IDEA and RC4
C. SSL and MD4
D. DES and RC4
Correct Answer: A QUESTION 164
What are the 3 main components of the IPS Event Analysis software Blade? i) Correlation Unit ii) Correlation Client iii) Correlation Server iv) Analyzer Server v) Analyzer Client vi) Analyzer Unit
A. i ii iii
B. iv, v. vi
C. i, iii, iv
D. i, iv, v
Correct Answer: D QUESTION 165
How can you verify that SecureXL is running?
A. cpstat os
B. fw ver
C. securexl stat
D. fwaccel stat
Correct Answer: D QUESTION 166
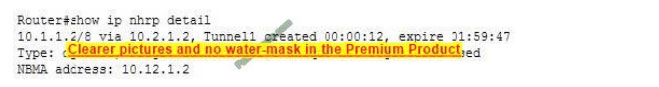
Susan needs to change the DNS settings on the SecurePlatform Gateway. Using the output below, which gateway she could edit from the devices view using Edit gateway, then selecting the DNS tab?
A. Seoul-Edge
B. Prague-GW
C. Berlin-GW
D. Paris-GW
Correct Answer: D QUESTION 167
What is the router command to save your OSPF configuration?
A. Save
B. write config
C. save memory
D. write mem
Correct Answer: B QUESTION 168
You enable Sweep scan Protection and Host port scan in IPS to determine n a large amount of traffic from a specific internal IP address is network attack, or a user’s system is infected with a worm. Will you get all the information you need from these actions?
A. No. To verify if tins is a worm or an active attack, you must also enable TCP attack defenses 70
B. No. The logs and alert can provide some level of information, but determining whether the attack is intentional or a worm requires further research.
C. Yes. IPS will limit the traffic impact from the scans, and identify if the pattern of the traffic matches any known worms
D. No. These PS protections will only block the traffic, but it will not provide a detailed analysis of the traffic
Correct Answer: B QUESTION 169
Using SmartProvisioning Profiles, which of the following could be configured for both SecurePlatform AND UTM-1 Edge devices? i) Backup ii) Routing iii) Interfaces iv) Hosts v) NTP server vi) DNS
A. ii, iii, iv, and vi
B. i, iii, iv, and vi
C. None of these options are available for both.
D. i, ii, and iv
Correct Answer: C QUESTION 170
What is the advantage for deploying Connectra in a DMZ, versus a LAN?
A. Connectra adds another layer of access security to internal resources, when It resides in a DMZ
B. B.SSL Network Extender is ineffective in a LAN deployment
C. Traffic is in clear text when forwarded to internal servers, but the back connection is encrypted 71 for remote users
D. Traffic is authenticated without hiding behind Connectra’s IP address
Correct Answer: A QUESTION 171
Your customer wishes to use SmartWorkflow Software Blade, but he also wishes to install a policy during an emergency without an approval. Is it possible? Select the BEST answer
A. Yes, it is possible but the administrator must receive special administrator permission i.e, can install in emergency. You can use the new CUI to set the administration security setting.
B. Yes, it is possible, but this feature must be configured in the Global Properties. The administrator must provide a special password and the reason for this emergency installation.
C. Yes. It is possible, but this feature must be configured in Global Properties and the administrator must provide a special password.
D. No, if a customer uses the SmartWorkflow Software Blade, o policy must be approved
Correct Answer: B QUESTION 172
Check Point product implements a Consolidation Policy?
A. Eventia Reporter
B. SmartView Monitor
C. SmartLSM
D. SmartView Tracker
Correct Answer: A QUESTION 173
Which of the following is not supported by CoreXL?
A. IPV4
B. IPS
C. Route-based VPN
D. SmartView Tracker
Correct Answer: C QUESTION 174
You have three Gateways in a mesh community. Each gateway’s VPN Domain is their internal network as defined on the Topology tab setting “All IP Addresses behind Gateway based on
73 Topology Information”
You want to test the route based VPN, so you created VTls among the Gateways and created static route entries for the VTTs However, when you test the VPN. You find out the VPN still go through the regular
domain IPSec tunnels instead of the routed VT1 tunnels.
What is the problem and haw do you make the VPN use the VII tunnels?
A. Route-based VTI takes precedence over the Domain VPN. Troubleshoot the static route entries to insure that they are correctly pointing to the VTI gateway IP
B. Domain VPN takes precedence over the route-based VTI to make the VPN go through VTI. use an empty group object as each Gateway’s VPN Domain
C. Domain VPN takes precedence over the route-based VTI. To make the VPN go through VTI. remove the Gateways out of the mesh community and replace with a star community
D. Route-based VTI takes precedence over the Domain VPN. To make the VPN go through VTI. Use dynamic-routing protocol like OSPF or BGP to route the VTI address to the peer instead of static routes
Correct Answer: B
QUESTION 175
The Management Portal Software Blade allows users to
A. View Security Policies
B. Monitor traffic flows
C. Add/Delete rules
D. Create/Modify objects
Correct Answer: A
QUESTION 176
You have configured an LDAP account unit and confirmed the Apply & Fetch Branches option works in Connectra, but end users still cannot be authenticated. What is the MOST LIKELY cause?
A. The Administrator’s login is incorrect.
B. The LOAP server is incorrectly configured
C. The user is not defined in Active Directory 74
D. The LOAP account unit’s login Distinguished Name is incorrectly configured
Correct Answer: D
QUESTION 177
After repairing a SmartWorkflow session:
A. The session moves to status Repaired and a new session can be started.
B. The session moves to status Awaiting Repair and must be resubmitted.
C. The session is continued with status not approved and a new session must be started.
D. The session is discarded and a new session is automatically started.
Correct Answer: A
QUESTION 178
The Management Portal allows all of the following EXCEPT:
A. View administrator activity
B. Schedule policy installation
C. View the status of Check Point products
D. Manage firewall logs
Correct Answer: B QUESTION 179
Which of the following functions CANNOT be performed in clinetinfo on computer information collected?
A. Copy the contents of the selected cells.
B. Save the information in the active tab to an .exe fife.
C. Enter new credential for accessing the computer information.
D. Run Google.com search using the contents of the selected cell.
Correct Answer: D
QUESTION 180
Your customer asks you about checkpoint SmartWorkflow. His company must comply with various laws and regulations and therefore it is important for him to be able to see the changes made to specific object. You explain to him that he can use the SmartWorkflow software Blade to achieve his objective and show him some examples (shown in Figures below). How can the customer receive the required information?
Choose the best answer
A. The customer can check compliance. This function compares the logs with the compliance requirements and automatically reports which part of the selected compliance is fulfilled and which is not
B. The customer can use the Check Point’s SmartView Tracker to view the required information. He selects the log category Changed Objects
C. The customer can use the Record Details. This feature enables administrators to track changes that have been made to objects over an extended period of time These changes are recorded in SmartView Tracker as audit togs
D. The customer can use the Check Point’s SmartView Tracker directly to receive the required information. He selects the log category SmartWorkflow
Correct Answer: B
QUESTION 181
When a security administrator logs in to SmartDashboard and selects Continue without session from the following window, what kind of access will be generated in SmartDashboard?
A. He will get read4 only access to the policy, network objects and session management
B. He will get read-only access to the policy and network objects; however, He can still manage the sessions, i.e. Approve, Request Repair etc
C. A new session will automatically be created with a default session name along with date and time. All changes made by the manager will be saved in this new session
D. No access will be granted, he will be logged out of SmartDashboard
Correct Answer: A
QUESTION 182
How do you control the maximum number of mail messages in a spool directory?
A. In the Gateway object’s SMTP settings under the Advanced window
B. In the smtp. conf file on the Security Management Server
C. In the Security Server window in Global Properties
D. In IPS SMTP settings
Correct Answer: A
QUESTION 183
Which of the following is TRUE concerning unnumbered VPN Tunnel Interfaces (VTls)?
A. VTls cannot be assigned a proxy interface.
B. Local IP addresses are not configured, remote IP addresses are configured.
C. VTls can only be physical, not loopback
D. VTls are only supported on the IPSO Operating System.
Correct Answer: B QUESTION 184
When using Connectra with endpoint Security Policies, what option is NOT available when configuring DAT enforcement?
A. Maximum DAT file version
B. Maximum DAT file age
C. Minimum DAT file version
D. Oldest DAT file timestamp
Correct Answer: A QUESTION 185
When configuring a web Application for SSL. VPN remote access, you have given the following definition for the application along with its protection level?
77 Which of the following is best match for the above application?
A. dmz.example.com/extranet
B. www.dmz.example.com
C. www.example.com/intranet
D. hr.dmz.example.com/intranet
Correct Answer: C QUESTION 186
The SmartProvisioning management concept is based on:
A. Zones
B. Groups
C. Regions
D. Profiles
Correct Answer: D QUESTION 187
You start the configuration of SmartWorkflow. SmartWorkflow is enabled, but you are not able to select Open new session because it is grayed out?
What must be done to open a new session?
A. Sessions in the Manage menu of SmartDashboard must be selected and enabled.
B. The use of sessions must be enabled by the CU command. SWF_session start.
C. A rule which allows the SmartWorkflow traffic must be placed on the top of the Rule Base.
D. The Work with sessions in Global Properties must be set.
Correct Answer: D QUESTION 188
Which operating system(s) support(s) unnumbered VPN Tunnel Interfaces (VTls) for route-based VPNs? 78
A. SecurePlatform for NGX and higher
B. Solaris 9 and higher
C. IPSO 3.9 and higher
D. Red Hat Linux
Correct Answer: A
QUESTION 189
If Bob wanted to create a Management high Availability configuration, what is the minimum number of Security management servers required in order to achieve his goal?
A. Three
B. Two
C. Four
D. One
Correct Answer: B
QUESTION 190
Match the SmartDashboard session status icons with the appropriate SmartWorkflow session status:
A. 1-A, 2-B, 3-C, 4-D, 5-E
B. 1-B, 2-A, 3-D, 4-E, 5-C
C. 1-C, 2-B, 3-A, 4-D, 5-E
D. 1-E, 2-D, 3-C, 4-B, 5-A 79
Correct Answer: B
QUESTION 191
What is a task of the IPS Event Analysis Client?
A. Add events to the events database.
B. Assign a severity level to an event.
C. Display the received events.
D. Analyze each IPS log entry as it enters the Log server
Correct Answer: C
QUESTION 192
When upgrading to NGX R65, which Check Point products do not require a license upgrade to be current?
A. None, all versions require a license upgrade
B. VPN-1 NGX(R64) and later
C. VPN-1 NGX(R60) and later
D. VPN-1 NG with Application Intelligence (R54) and later
Correct Answer: C
QUESTION 193
A security audit has determined that your unpatched web application server is revealing the fact that it accesses a SQL server. You believe that you have enabled the proper SmartDefense setting but would like to verily this fact using SmartView Tracker. Which of the following entries confirms the proper blocking of this leaked information to an attacker?
A. “Fingerprint Scrambling: Changed [SQL] to [Perl]”
B. “HTTP response spoofing: remove signature [SQL Server]”
C. “Concealed HTTP response [SQL Server]. (Error Code WSE0160003)”
D. “ASCII Only Response Header detected: SQL” 80
Correct Answer: C
QUESTION 194
Where is it necessary to configure historical records in SmartView Monitor to generate Express reports in Eventia Reporter?
A. In SmartDashboard, the SmartView Monitor page in the VPN-1 Security Gateway object
B. In Eventia Reporter, under Express > Network Activity
C. In Eventia Reporter, under Standard > Custom
D. In SmartView Monitor, under Global Properties > Log and Masters
Correct Answer: A
QUESTION 195
Where do you enable popup alerts for SmartDefense settings that have detected suspicious activity?
A. In SmartView Monitor, select Tools > Alerts
B. In SmartView Tracker, select Tools > Custom Commands
C. In SmartDashboard, edit the Gateway object, select SmartDefense > Alerts
D. In SmartDashboard, select Global Properties > Log and Alert > Alert Commands
Correct Answer: A
QUESTION 196
When configuring VPN High Availability (HA) with MEP, which of the following is correct?
A. The decision on which MEP Security Gateway to use is made on the remote gateway’s side (non-MEP side).
B. MEP Gateways must be managed by the same Smart Center Server.
C. MEP VPN Gateways cannot be geographically separated machines.
D. If one Gateway fails, the synchronized connection fails over to another Gateway and the connection
continues
81
Correct Answer: A
QUESTION 197
Which of the following would NOT be a reason for beginning with a fresh installation of VPN-1 NGX R65, instead of upgrading a previous version to VPN-1 NGX R65?
A. You see a more logical way to organize your rules and objects.
B. YOU want to keep your Check Point configuration.
C. Your Security Policy includes rules and objects whose purpose you do not know.
D. Objects and rules’ naming conventions have changed overtime.
Correct Answer: B QUESTION 198
How do you block some seldom-used FTP commands, such as CWD, and FIND from passing through the Gateway?
A. Use FTP Security Server settings in SmartDefense.
B. Add the restricted commands to the aftpd.conf file in the Smart Center Server.
C. Configure the restricted FTP commands in the Security Servers screen of the Global properties.
D. Enable FTP Bounce checking in SmartDefense.
Correct Answer: A
QUESTION 199
Match each of the following commands to their correct function. Each command only has one function listed
A. C1>F6; C2>F4; C3>F2; C4>F5
B. C1>F4; C2>F6; C3>F3; C4>F2
C. C1>F2; C2>F4; C3>F1; C4>F5
D. C1>F2; C2>F1; C3>F6; C4>F4
Correct Answer: A QUESTION 200
Which NGX R65 logs can you configure to send to DShield.org?
A. SNMP and account logs
B. Alert and user-defined alert logs
C. Account and alert logs
D. Audit and alert logs
Correct Answer: B QUESTION 201
The customer has a small Check Point installation which includes one Window XP workstation working as SmartConsole ,, one Solaris server working as SmartCenter, and a third server running SecurePlatform working as Security Gateway. This is an example of:
A. Hybrid Installation
B. Unsupported configuration
C. Stand-Alone Installation
D. Distributed Installation
Correct Answer: A
QUESTION 202
Which VPN-1 NGX R65 component displays the number of packets accepted, rejected, and dropped on a specific Security Gateway, in real time?
A. SmarrViewMonitor
B. SmarrView Status
C. SmartUpdate
D. Eventia Analyzer
Correct Answer: A
QUESTION 203
SmartDefense profiles are:
A. Files that take 3MB of RAM from the user console machine.
B. Able to be cloned, but only from the command line.
C. Configurable up to 20 for all VPN-1 R65 Gateways and above.
D. Configurable from either the SmartDefense tab or from the Gateway itself.
Correct Answer: D
QUESTION 204
What is a Consolidation Policy?
A. A global Policy used to share a common enforcement policy for multiple similar Security Gateways
B. The collective name of the logs generated by Eventia Reporter
C. The collective name of the Security Policy, Address Translation, and SmartDefense Policies
D. The specific Policy written in SmartDashboard to configure which log data is stored in the Eventia Reporter database
Correct Answer: D
QUESTION 205
Match the ClusterXL Modes with their configurations A. A2.B3.C4.D 1
B. A2.B3.C 1.D4
C. A3,B2, C4,D 1
D. A3.B2.C 1.D4
Correct Answer: D
QUESTION 206
State Synchronization is enabled on both members in a cluster, and the Security Policy is successfully installed. No protocols or services have been deselected for “selective sync”. The following is the fw tab -t connections -s output from both members:Is State Synchronization working properly between the two members?
A. Members A and B are synchronized, because #SLINKS are identical in the connections table.
B. Members A and B are not synchronized, because #VALS in the connections table are not close.
C. Members A and B are not synchronized, because #PEAKfor both members is not close in the connections table.
D. Members A and B are synchronized, because ID for both members is identical in the connections table.
Correct Answer: B
QUESTION 207
Which of the following is TRUE concerning numbered VPN Tunnel Interfaces (VTIs)?
A. VTIs are supported on SecurePlatform Pro.
B. VTIS cannot share IP addresses
C. VTIs can use an already existing physical-interface IP address
D. VTIS are assigned only local addresses, not remote addresses
Correct Answer: A QUESTION 208
Which of the following is NOT supported with Office Mode?
A. SSL Network Extender
B. L2TP
C. Secure Client
D. Transparent Mode
Correct Answer: D QUESTION 209
Central License management allows a Security Administrator to perform which of the following functions?
(1)
Check for expired licenses.
(2)
Sort licenses and view license properties.
(3)
Attach both NGX Central and Local licenses to a remote module.
(4)
Delete both NGX Local licenses and Central licenses from a remote module.
(5)
Add or remove a license to or from the license repository.
(6)
Attach and/or delete only NGX Central licenses to a remote module (not Local licenses).
A.
1, 2, 3, 4, & 5 87
B.
1. 2. 5. & 6
C.
2, 3, 4, & 5
D.
2, 5, & 6
Correct Answer: A QUESTION 210
You are the Security Administrator for a university. The university’s FTP servers have old hardware and software. Certain FTP commands cause the FTP servers to malfunction. Upgrading the FTP servers is not an option at this time. Where can you define Blocked FTP Commands passing through the Security Gateway protecting the FTP servers?
A. SmartDefense > Application Intelligence > FTP > FTP Security Server
B. Rule Base > Action Field > Properties
C. FTP Service Object > Advanced > Blocked FTP Commands
D. Global Properties > Security Server > Allowed FTP Commands
Correct Answer: A
Flydumps ensures that the first time you take the exam will be able to pass the exam to obtain the exam certification. Because Checkpoint 156-915 provide to you the highest quality analog Checkpoint 156-915 Exam will take you into the exam step by step. Flydumps guarantee that Latest Checkpoint 156-915 exam help you to pass the exam successfully.
Welcome to download the newest Examwind 220-010 dumps: http://www.examwind.com/220-010.html
http://www.alnaba.org/oracle-cx-310-019-guide-provider-50-off-oracle-cx-310-019-certification-exam-for-download/