Welcome to download the newest Dumpsoon MB2-700 VCE dumps: http://www.dumpsoon.com/MB2-700.html
Good News!The Flydumps Cisco 350-029 exam questions and answers covers all the knowledge points of the real exam. With our Cisco 350-029 practice test, you will never worry about the exam.Recently the new version with all new updated Cisco 350-029 exam dumps can free download on the site Flydumps.com.Visit the site to get more exam information.
QUESTION 51
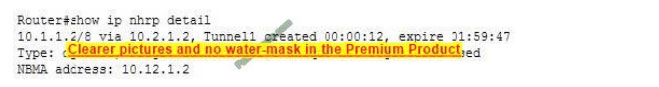
Referring to the exhibit, if RTP header compression is used on the link, the header??s overhead on the voice packet will be reduced by what percent?
A. from 50% to 25%
B. from 50% to 20%
C. from 70% to 20%
D. from 70% to 33%
Correct Answer: D
QUESTION 52
Which two statements are correct?
A. A VC type 5 transports a VLAN over MPLS.
B. A VC type 4 tunnels an Ethernet port over MPLS.
C. A VC type 5 tunnels an Ethernet port over MPLS.
D. A VC type 4 transports a VLAN over MPLS.
Correct Answer: CD
QUESTION 53
Which of the following technologies can improve convergence time following a link failure in a service provider network? (Choose two.)
A. RSVP
B. MPLS TE FR
C. MPLS VPN
D. SNMP
E. BFD
F. VPLS
Correct Answer: BE
QUESTION 54
Which of the following statemets regarding Control Plane Policing (CoPP) is correct? (Choose three.)
A. Control Plane Policing (CoPP) addresses the need to protect the management planes, ensuring routing stability, availability, and critical packet delivery.
B. Control Plane Policing (CoPP) leverages MQC to define traffic classification criteria and to specify configurable policy actions for the classified traffic.
C. Control Plane Policing (CoPP) uses a dedicated “control-plane” command via the Modular QoS CLI (MQC) to provide filtering and rate limiting capabilities.
D. Control Plane Policing (CoPP) uses “service policy” command under relevant interfaces to filter DOS packet to protect routing packets.
E. Control Plane Policing (CoPP) protects the transit management and data traffic through the router.
Correct Answer: ABC
QUESTION 55
Which two statements are correct with regard to route distinguisher as defined in RFC 4364-AKA IP-VPN (MPLS-VPN)?
A. The configuration to define Route-Distinguisher is Ip vrf bulle Rd 1:1
B. A route distinguisher can be imported and exported to and from a VRF
C. Route-Distinguisher is an 8 byte BGP attribute value used in influencing BGP best path algorithm.
D. Route-Distinguisher is an 8 byte value used in creating unique VPNv4 address.
Correct Answer: AD
QUESTION 56
Which two statemets are true?
A. DPT/RPR uses a bi-directional ring consisting of two symmetric counter rotating fibre rings.
B. DPT/RPR is defined in the IEEE 802.17 standard and it uses Token Bucket system to avoid collisions on the fiber.
C. DPT/RPR can be deployed in the Core of the SP networks where point-to-point POS links are used to make best use of the Bandwidth.
D. In DPT/RPR rings, data packets can be sent in one direction (downstream) and the corresponding control packets in the opposite direction (upstream), thus using both fibres concurrently to maximise bandwidth.
Correct Answer: AD
QUESTION 57
Which statements about MPLS Label Distribution Protocol(LDP) are valid? (Choose three.)
A. LDP hello packets are sent to UDP port 646
B. LDP hello packets are sent to TCP port 711
C. LDP sessions are TCP sessions to port 646
D. LDP sessions are TCP sessions to port 711
E. LDP establishes a peer relationship with another router that must be directly attached.
F. LDP can establishes a peer relationship with another router that is not directly attached
Correct Answer: ACF
QUESTION 58
How would you characterize the source and type in a denial of service attack on a router?
A. By perfornubg a show ip interface to see the type and source of the attack based upon the access-list matches
B. By setting up an access-list to permit all ICMP ,TCP ,and UDP traffic with the log or log-input commands ,then use the show access-list and show log commands to determine the type and source of attack
C. By performing a show interface to see the transmitted load “txload” and receive load “rxload” ;if the interface utilization is not maxed out ,there is no attack underway
D. By applying an access-list to all incoming and outgoing interfaces,turning off route- cache on all interfaces,then,when telnetting into the router perform a debug IP packet detail
Correct Answer: B
QUESTION 59
Which of the following IOS commands cause syslog messages to be stamped with time and dates?
A. logging datetime on
B. service timestamps log datetime
C. service logging datetime
D. logging timestamps on
E. logging trap datetime
Correct Answer: B
QUESTION 60
In the context of GMPLS,LMP stands for;
A. None of above
B. Label Management Protocol
C. Loop Management Protocol
D. Link Management Protocol
E. Load Management Protocol
Correct Answer: D
QUESTION 61
Which of the following statements is correct regarding PIM Sparse Mode operations?
A. Receivers are “registered” with RP by their first-hop router.
B. It supports shared trees only assuming all hosts want the multicast traffic.
C. From the RP, traffic flows down a Source Tree to each receiver.
D. It does not support all underlying unicast routing protocols like GBP.
E. Receivers are “joined” to the Shared Tree (rooted the rp ) by their local Designated Router (DR).
Correct Answer: E
QUESTION 62
Which statements are correct for forwarding traffic into MPLS TE tunnels? (Choose three)
A. Autoroute causes the tunnel to be treated as a directly connected link to the head-end.
B. Autoroute causes the TE head-end to establish IGP adjacency with the tail-end over the tunnel.
C. Forwarding adjacency makes the TE head-end node advertise the Tunnel LSP into the IGP.
D. Forwarding adjacency supports unequal cost load balancing over multiple TE tunnels.
Correct Answer: ACD
QUESTION 63
Select two valid administratively scoped multicast addresses in networks running Interior Gateway protocols like EIGRP and OSPF
A. 239.255.255.255
B. 224.0.0.10
C. 239.0.0.1
D. 224.0.0.5
Correct Answer: AC
QUESTION 64
In which of the following lists of APS Action Requests is the priority correctly arranged from lowest to highest?
A. Wait-to-Restore, Manual Switch, Forced Switch, Lockout of Protection
B. Wait-to-Restore, Forced Switch, Manual Switch, Lockout of Protection.
C. Manual Switch, Wait-to-Restore, Lockout of Protection, Forced Switch.
D. Lockout of Protection, Forced Switch, Manual Switch, Wait-to-Restore
E. Lockout of Protection, Manual Switch, Forced Switch, Wait-to-Restore
F. Wait-to-Restore, Manual Switch, Lockout of Protection, Forced Switch
Correct Answer: A
QUESTION 65
What is the action of “pop” in the context of MPLS switching?
A. It replaces the top label in the MPLS label stack with a set of labels.
B. It replaces the top label in the MPLS label stack with another value.
C. None of above.
D. It removes the top label in the MPLS label stack.
E. It adds a top label in MPLS label stack.
Correct Answer: D
QUESTION 66
What is the encapsulation mode for MPLS running on Ethernet?
A. Transparent mode.
B. Frame mode
C. Channel mode
D. Packet mode.
E. Tunnel mode.
Correct Answer: B
QUESTION 67
The show ip ospf database external command displays information about which OSPF LSA type?
A. LSA type 1
B. LSA type 2
C. LSA type 7
D. LSA type 3
E. LSA type 9
F. LSA type 5
Correct Answer: F
QUESTION 68
Forwarding Equivalence Class (FEC) corresponds to: (Choose four.)
A. Layer 2 circuits (ATM, FR, PPP, HDLC, Ethernet)
B. Groups of addresses/sites-VPN x
C. IPSEC Encryption Algorithm
D. A bridge/switch instance-VSI
E. Tunnel interface-traffic engineering
Correct Answer: ABDE
QUESTION 69
The mechanisms for distributing LDP are:
A. CEF and the FIB table
B. UDP and IP
C. A and B
D. RSVP and CEF
E. LDP and RSVP
Correct Answer: E
QUESTION 70
Which two statements are true about RPF checks in MSDP (Multicast Source Discovery Protocol)?
A. It prevents message looping, Session Advertisement (SA) messages must be RPF checked.
B. RPF check should be done against the route to the Rendez-vous Point of the corresponding PIM-SM domain, which originated the SA.
C. RPF checking Session Advertisement (SA) messages will cause message looping.
D. RPF check should be done against the route to the source S of the corresponding PIM-SM domain.
Correct Answer: AB
QUESTION 71
BGP best route selection process is based on what?
A. path attributes
B. lowest cost
C. highest bandwidth
D. lowest delay
E. lowest hop-count
Correct Answer: A
QUESTION 72
Pick the 4 valid ATM Cell Header fields:
A. GFC-4 bits of generic flow control
B. Forward-explicit congestion notification(FECN)
C. VCI-16 bits of virtual channel identifier
D. CLP-1 bit of congestion loss
E. HEC-8 bit of header error control
F. ATM Discard Eligibility(DE) bit
Correct Answer: ACDE
QUESTION 73
A network administrator wants to detect a login attack against a router. What IOS command can make the attack recorded in syslog server?
A. Login detect login-failure log
B. none of the above
C. Logging detect fail-login
D. Login on-failure log
E. Logging login on-failure
Correct Answer: D
QUESTION 74
R3 and R4 are Route-Reflectors and there is an I-BGP session between them, there is NO I-BGP session between R1 and R2. For an External Route from CE-2 in R2 to reach R1, which two statements are true? (Choose two.)
A. R1, R3 and R4 establish full mesh I-BGP sessions, R2, R3 and R4 establish full mesh I-BGP sessions.
B. R1 acts as a Route-Reflector client to R3, R2 acts as a Route-Reflector client to R4.
C. R1 acts as a Route-Reflector client to R4, R4 acts as a Route-Reflector client to R4, R2 acts as a Route-Reflector client to R3.
D. CE-2 establishes multi-hop E-BGP sessions with R3 and R4.
Correct Answer: BC
QUESTION 75
With the BGP peerings shown, which three solutions are most correct?
A. rtrA and rtrD are route-reflector-clients; rtrB and rtrC are route reflectors part of the same cluster.
B. rtrA and rtrD are route-reflector-clients; rtrB and rtrC are route reflectors part of the different cluster.
C. rtrA, rtrB and rtrC are part of a confederation sub-AS and rtrD is part of a different confederation sub-AS
D. rtrA, rtrB are part of one confederation sub-AS and rtrC,rtrD are part of a different confederation sub-AS
E. rtrA, rtrB and rtrC are part of a confederation sub-AS where rtrB is a route reflector and rtrA, rtrC are route-reflector-clients.
Correct Answer: BDE
QUESTION 76
In Multicast VPN (MVPN) implementations, which two of the following statements are regarding the Default MDT Group? (Choose two.)
A. It is used for PIM control traffic.
B. It is optionally configured for a high bandwidth multicast source to reduce multicast traffic replication to uninterested PE routers.
C. Within the VPF configuration in the PE router, multiple Default MDT groups are configured so each VPF can support multiple multicast sources.
D. There is a reduced multicast state in the MPLS core P routers.
E. When multicast traffic exceeds a certain configured threshold, traffic from the Data MDT is switched to the Default MDT to conserve bandwidth.
Correct Answer: AD
QUESTION 77
VoIP bearer traffic is typically marked to which DSCP value ?
A. af41
B. af31
C. 0 (default )
D. cs7
E. cs3
F. ef
Correct Answer: F
Flydumps.com will provide you with the most updates material to prepare for the tests all the Cisco 350-029 torrent are available at the site. Studying with dumps makes it much easier to pass the certification. Number of networking downloads including the Cisco 350-029 download are available on the website. Various websites offering such information have information in various formats you can easily download the format that is suitable for you it can be in Cisco 350-029 Testing Engine or in html.
Dumpsoon MB2-703 dumps with PDF + Premium VCE + VCE Simulator: http://www.dumpsoon.com/MB2-703.html